git Directory Exposure on apply.dinus.ac.id
Hello everyone,
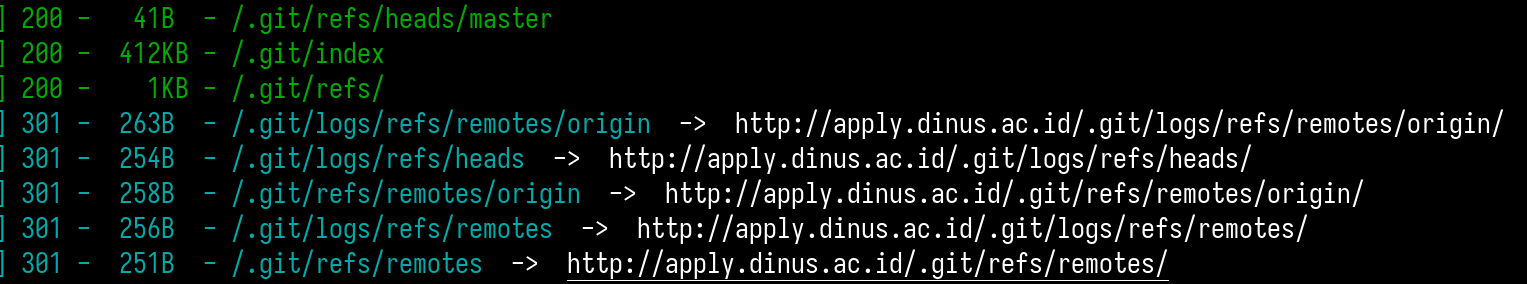
I want to share a security finding on a registration website of one university in Indonesia. While inspecting their production environment, I discovered that the .git directory was still publicly accessible.
This poses a serious security risk because an attacker could reconstruct the repository and extract sensitive information or credentials left in the development history.
During my validation and data extraction attempts, I was able to retrieve the application’s source code, critical credentials such as SMTP details, and even sensitive files like ID cards.
Note: It is crucial to implement clean and automated deployment processes to prevent such exposures.
I have responsibly reported this issue to the relevant team, and it has since been resolved.
